Why Must You as A Marketer Implement Conversions API (CAPI)?
Understanding the Impact of Third-Party Cookie Loss
Third-party cookies are web cookies that are placed on a website by the owner (third-party) to track and collect a user’s purchasing behavior. They are also referred to as tracking cookies, tracking codes, and tracking pixels, and are mainly used for cross-site identification. The information being stored can range from individual IP addresses, search and browser history, products and websites viewed, and other specific details about devices.
The Problem?
Users are often unaware that their data is being collected and harvested from third-party cookies. The lack of self-regulation caused governments from various countries to introduce privacy laws – this led to stringent regulation around data privacy and user consent – the GDPR and CCPA.
The Rise of Regulations

Regulations around user privacy, such as EU’s GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) have been put in place to monitor and regulate the personal information being collected and stored by companies online.
Apple gave their users the option to opt out of being tracked across applications, ensuring they were in line with regulations. Mozilla’s Firefox and Meta adopted a similar approach. Most recently Google announced its plans to phase out third-party cookies from Chrome.
The move posed new challenges for marketers when it came down to being able to track and infer from their Ad spending. This resulted in the urgent need for a solution that was reliable and mostly regulation compliant. This led to the quick acceptance and adoption of first-party data.
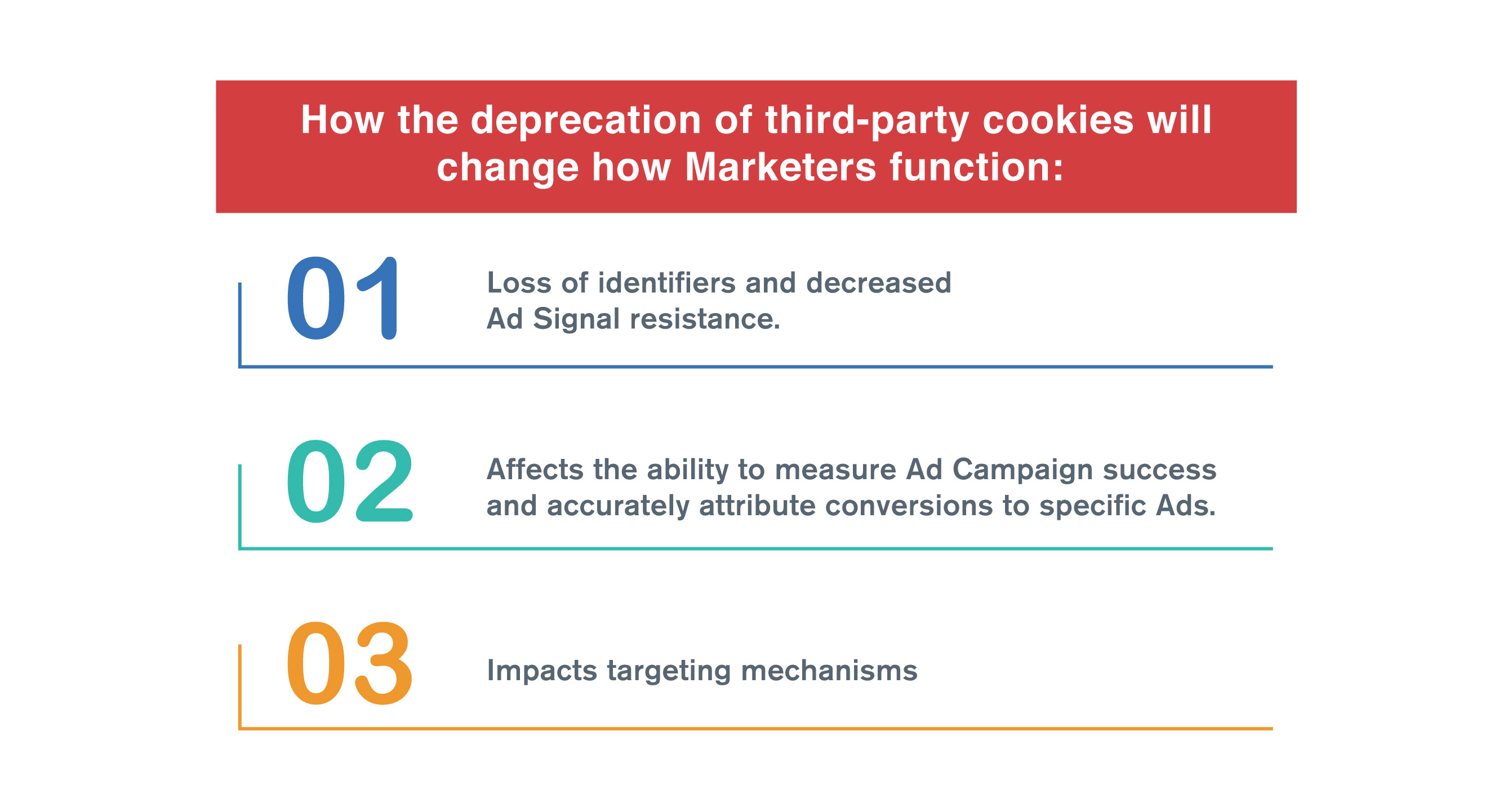
The third-party cookie demise has greatly influenced marketers and their ability to go about day-to-day functions in digital marketing. The rise of restrictions on user tracking has impacted the way digital Ads are Targeted, Measured, and Optimized.
How does Conversions API work?
Conversions API (CAPI), also known as server-side tracking allows marketers to send Web events from their servers directly to their respective Ad platforms. CAPI is designed to create a connection between an advertiser’s marketing data (such as website events, app events, and offline conversions) from an advertiser’s server, website platform, mobile app, or CRM to the advertising channel (Meta, Snapchat, TikTok, etc.) to further optimize Ad targeting efforts and decrease the cost per result, and measure outcomes.
Why Implement CAPI?
Once you implement CAPI, you’ll be able to track more conversions, which will give you more insight into your Ad campaign performance and will allow your marketing platform’s algorithms to optimize everything from audiences to budgeting to bidding more effectively. Advertisers who stick with the core Pixel approach will have less insight into post-click actions of all kinds, most importantly, sales, signups, and leads.
Another issue addressed by server-side tracking is the broader industry’s move away from browser cookies as the method of delivering Ad-tracking information. Server-side tracking is not reliant on browser cookies to capture data, so moving to CAPI now will also keep you ahead of the curve.
Benefits of Implementing Conversions API
Reduce Cost per Action

Data from the Conversions API is less affected than the Meta pixel by browser loading errors, connectivity issues, and Adblockers. When you use the Conversions API alongside the pixel, it creates a reliable connection that helps the delivery system decrease your cost per action. Reduce your ‘Cost Per Action’ as a result of increased event matching. Your marketing data is most effective when it can be matched with accounts across Meta technologies. With the Conversions API, you can include additional customer information parameters that help increase matched events and your event match quality.
Optimise Ads for actions that happen later in the customer’s journey. Examples of these events include actions that happen after a purchase (such as subscriptions), actions that happen in shops, or even customer scores. This information helps Ad platforms show your ads to customers who are more likely to be profitable and generate value for your business.
Improve Measurement
The Conversions API can help you better measure Ad performance and attribution across your customer’s full journey, from discovery to conversion. This helps you understand how digital advertising affects both online and offline results.
Increase data control. When implemented separately from the pixel, Conversions API gives you more control over what you share and when you share it.
Advertisers have been asking for a solution to reduce Pixel’s effectiveness, and CAPI is the answer. Conversions API improves measurement and attribution across the full funnel, giving more visibility into the impact of digital advertising on cross-channel results. Currently, users can see Pixel and Conversions API data in Meta Events Manager with aggregation in the Aggregated Events Measurement tab.
Lead Quality Level Up
Lead generation advertisers know the struggle to obtain leads both in quality and quantity. By using a post-conversion event with Conversions API, advertisers can factor in leads that have actually converted into a sale/subscription/etc to campaign optimization.
Why Work with A First-Party Data Enabler That Allows First-Party Data Implementations Across Multiple Platforms at One Go?
Enabling first-party data can mean heavy investment in terms of infrastructure, money, time, and IT resources. Imagine a SaaS B2B solution that equips brands, agencies, and marketers with solutions that are fast and secure, giving the marketer complete control and access to first-party data within minutes.
At Datahash, our goal has been to enable our stakeholders across the board to be able to target, deliver and measure their digital advertising efforts without compromising on your ‘Data Signals’ and ‘Cost Per Lead.’
How Is Datahash Compliant?
This is the most common question any advertiser, or agency may have. How can passing first-party data be in check with privacy controls like GDPR, CCPA, or any user safety in general?
End-to-end Data Encryption using SHA256
SHA 256 is a keyless, one-way, and the most standard encryption across the internet. Once first-party data is encrypted using SHA256, no one including any tool or Ad-platform can ever convert it back to its raw format. With SHA256 you’re ensuring that all the data sent back to Ad-platforms via CAPI can only be used for users who are users of that Ad-platform.
No Data Storage
Datahash does not store any data, and any data passing through is encrypted on the SHA256 one-way encrypted events to Ad-platforms. With no storage, any GDPR or equivalent request is fulfilled with compliance in place.
Data Residency
EU Advertisers using Datahash are ensured that any data received from their sources never leave EU – Datahash is hosted and managed within EU premises.
On-Prem Option
Data-sensitive advertisers further have the option to use an enterprise version of Datahash which can be hosted on their own AWS cloud for full control and maximum security.
If you’d like to get started with Datahash, learn more here.
Data Privacy and Data Security are separate but overlapping disciplines that must work together to build and maintain trust. Approach: Recognize differences while supporting mutual goals What concerns security professionals Data security teams focus on confidentiality, integrity, availability, and resilience of data environments.
It is often technical and prescriptive, requiring a thorough understanding of system interactions and configurations similar to:
● Confidentiality: Access to valuable business information which may or may not relate to an identified or identifiable individual. Per the Security Safeguards Principle, confidentiality helps prevent the unauthorized viewing or disclosure of personal data. Worst case scenarios lead to personal data breaches and harms like identity theft.
● Integrity: Keeping data authentic, accurate, and reliable for its intended uses. Per the Data Quality Principle, integrity is the means by which data can be kept correct and current. Data tampering and corruption can lead to a range of harms if that data is used to make legal, professional, or financial decisions about an individual.
● Availability: Applies to Security (and IT) ensuring that information systems function properly so that business and personal data could be used by the organization when needed. Taking steps to recover mission-critical data in case of a fire in one of your server rooms is just one example. Per the Accountability Principle, not having availability safeguards in place can in itself be a data protection violation.
What concerns privacy professionals
Data privacy focuses on the collection, use, analysis, and disclosure of personal data. Digital business models bring about particular concerns which revolve around:
● Identifiability: The ways in which an individual, or their browser or device, can be singled out. For example, your name alone may not be enough to identify you as a customer, together with your email address and account ID you can easily be.
● Linkability: The ways in which information can be associated with an individual or stitched together to learn or infer more about the person. When you hear terms like identity graphs, single-customer-view, profiling, and targeting, data linkage is involved.
● Secondary uses: Where personal data is used for something other than it was originally collected, which can lead to unexpected, unwanted, and potentially negative outcomes. For example, if a website publisher sells your contact information to a data broker, you may start receiving time-wasting junk mail and email spam.
● Disclosure to third parties: As much a concern for Security as it is for Privacy teams, it is important to have trust in one’s suppliers, service providers and business partners. If you share your customers’ personal data with another organization, you are responsible for ensuring privacy principles and applicable obligations can be met.
● Unawareness: This is a whole-business problem. Employees handling personal data should be trained on their privacy and data protection responsibilities. But this implies the business should know what those responsibilities are. Awareness starts with understanding what applies to you.
● Privacy harms: Is personal data being used correctly? How can individuals be harmed if their data is misused or abused? Harms can be minor inconveniences like cleaning out spam emails to major consequences of having your identity stolen. Cybercriminals’ goals are often to steal a company’s most valuable information which is not only trade secrets.
Security and Privacy teams care deeply about preventing personal data breaches, and doing what it takes to ensure unauthorized parties keep their mitts off. With the above in mind, it’s easy to see how security and privacy share many principles and goals. This is one of the reasons minimum security requirements are included in data privacy laws, and why the GDPR enshrines “[personal] data protection by design.
Underestimating the risk of non-compliance

Besides GDPR, California’s CCPA, Canada’s PIPEDA, China’s PIPL, and Brazil’s LGPD are just a sampling of the comprehensive data privacy laws in effect today. Virginia, Colorado, Utah and Connecticut passed their own privacy laws, and Canada and the United Kingdom are looking at fresh legislative renovations. (Don’t worry, we’ll cover this alphabet soup in the next section.)
Each regime has enforcement mechanisms that can expose your business to potential administrative penalties, and in some cases private lawsuits. Penalties can be staggering. For example, European data protection authorities can fine an organization up to 4% of their annual global revenues. Penalties can also stack up. The California Privacy Rights Act gives the Privacy Protection Agency powers to fine businesses up to $2,500 per violation or $7,500 per intentional violation.